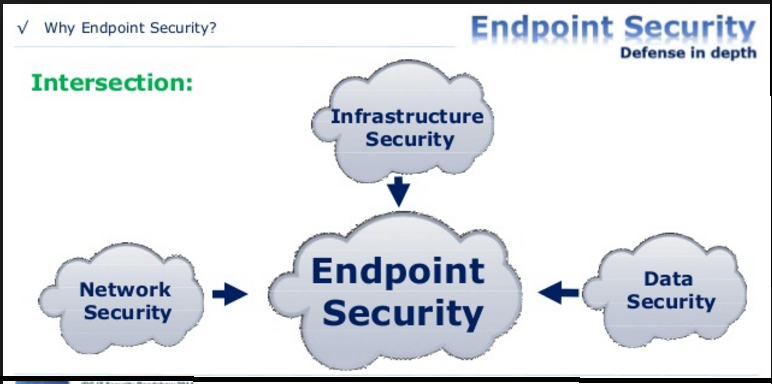
Symantec product threat protection achieves a higher level of security. Protect against most advanced threats with complete protection from endpoint to mail to servers to cloud. Endpoint protection provides everything from file reputation and behavioral analysis to advanced machine learning AI. With Symantec, you can secure and manage all of your endpoint devices and systems seamlessly, whether inside or outside your corporate network.
» Consulting on how best to use protection system for corporate network, endpoint devices and servers.
» We help corporate significantly reduce the number of network attacks by recommending right endpoint solution that fits into their requirement.
» We examine many distinct sources of data and try to "connect the dots" to find that "needle in a haystack" in the environment.
» Uncovers, prioritizes, and remediates for advanced & complex attacks across endpoint, email, network and web.
» Identify whether organization is under targeted attacks and automatically search for Indicators-of-Compromise with Intelligence tools
» Detect and investigate suspicious events via unique sandboxing and payload detonation capability
» We provide in-depth threat visibility across IT environments.
» Quickly isolate any compromised system from the enterprise network
» Optimize and customize customer's incident response flow with public API and integration with Splunk and 3rd party products.
iSAP offers more powerful, flexible Backup Solution to protect your corporate data. Data protection that goes beyond backup and recovery. iSAP partner with Veritas to provide robust data protection that helps any organization migrate their data to cloud, that gives an immediate protection for Windows Servers and enables time, cost and resource savings across your entire infrastructure.
With nearly every IT environment running virtual machines, ensuring protection of those machines has leapt to the top of iSAP priority. To solve this quandary, look no further than Symantec's Backup Exec Solution, the industry's gold standard in unified backup and recovery, which can dramatically reduce recovery time from data loss or major disasters while protecting all of your virtual machines and physical servers.
Not only does Backup Exec do all of that, it also allows individual file, folder, and granular object level recovery, integrated data duplication, disaster recovery, replication and centralized management. In short, you'll never have to worry about protecting your virtual machines again.
iSAP has extensive expertise with Backup Exec software and appliances. Our consultants are fully trained and ready to assist with a full range of Backup Exec data protection tasks.
» We help you to design your Backup Solution to maximize your data protection, ensure that this is conducted in a smooth and reliable fashion while maintaining day-to-day data protection standards.
» We help our customer's to assist with detailed Disaster Recovery and Business Continuity planning. Services include identification of critical system, technology and process recommendations, detailed cost analysis and ROI, plan documentation and DR plan implementation and testing.
» We advise in updating DR plans and strategy to fully leverage Backup Exec capabilities, enabling improved RPO and RTO.
» We maximize the investment in Backup Exec by properly implementing the full suite of Backup Exec features and functionality.
» We can review your existing backup Exec architecture and provide recommendations for improvements in design and implementation.

» a. Would your business survive if head office wasn't there tomorrow?
» b. If you lost your computer room today - who would call the helpdesk first?
» c. For what application would they be calling?
» d. Is that application adequately protected?
» e. How often do you back up that application?
» f. If you had to recover the data for that application from last night's backup - how long would it take?
» g. How long would it take you to then re-create the data for that application from last night's backup to the point before the crash/failure?
» h. Could you re-create it or would there be data loss?
» i. How many $ per hour or day would it cost your business if you could not access your business-critical applications?
» j. How many days/weeks without data access before your business fails?
» k. Who would be held responsible?